By bringing together the top 80 Executives in the region, we will discuss the most pressing Technology and Leadership challenges we face in an ever-evolving corporate landscape.
Over the next two and a half days, we will nurture meaningful relationships and tackle the challenges inherent to IT in a smaller, more dynamic setting. You will learn from your peers through various workshops, panels, roundtables and presentations. Our closed-door policy fosters an environment where all discussions are confined within the Forum walls, enabling more genuine and engaged conversations.
Learn about the latest and most innovative technologies that can bridge some of your organizational gaps through qualified one-on-one engagements, scheduled strategically throughout the Forum and selected by you, based on your most pressing needs.
Build new relationships and nurture existing ones, share in your successes and commiserate in the challenges that we all face as IT Leaders.
Join us for the West IT & Security Leaders Forum and leave ready to inspire action within your Organization!

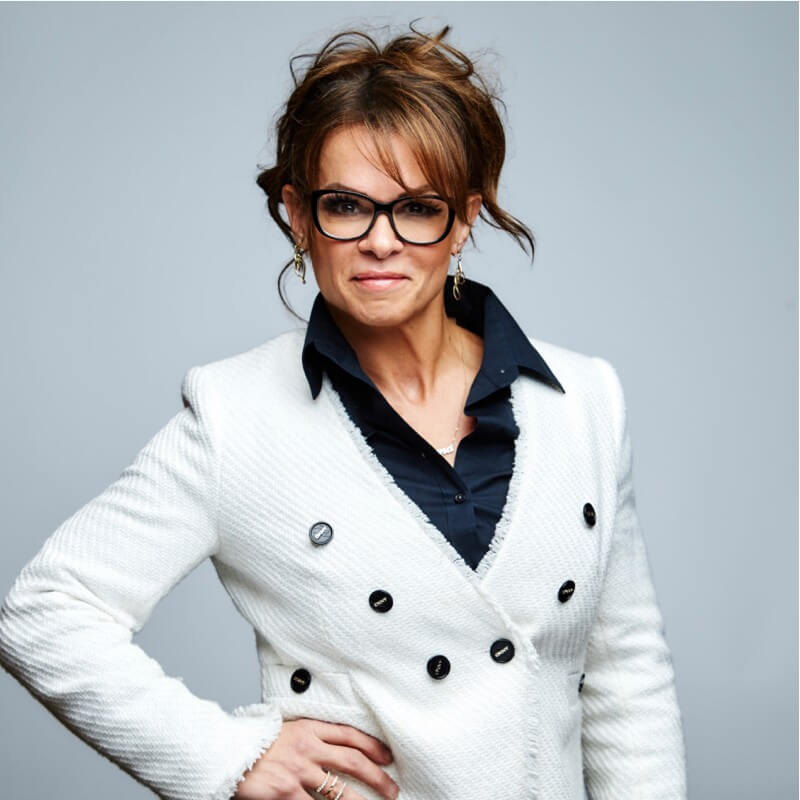
Master of Ceremonies
Shawnna DelHierro
Chief Technology Officer Recently of Sportsman Warehouse
Pendry Park City
Pendry Park City is a contemporary mountain enclave bringing the mastery of Utah’s awe-inspiring landscape to new heights. A ski-in / ski-out resort nestled in the center of Canyons Village, the slopeside retreat’s modernist design, luxury service, and thoughtful amenities will help ensure an exceptional experience.
Forum Agenda
Agenda may be subject to change. Click on each day to view full agenda.
2:00 PM - 5:00 PM MST
FORUM REGISTRATION & APP DEMONSTRATION
Get familiar with SINC Staff and the event layout. Secure your complimentary Swag Bag and learn how to use the Onsite Application for Peer Engagement and win great prizes!
5:30 PM - 7:00 PM MST
SINC WELCOME NETWORKING RECEPTION
Engage your Peers over canapes and cocktails
7:00 PM - 9:00 PM MST
SINC NETWORKING & ENGAGEMENT DINNER
7:00 AM - 7:55 AM MST
SINC IT LEADERS NETWORKING BREAKFAST
Full breakfast and lots of coffee available!
8:00 AM - 8:05 AM MST
SINC OPENING REMARKS
A Thank You from SINC – setting the tone for a great day!
8:05 AM - 8:45 AM MST
PANEL - The CIO's Role in the Future of Work
As organizations adapt to technological advancements, remote collaboration tools, and changing workforce dynamics, the CIO emerges as a key strategist, orchestrating digital transformation initiatives and ensuring seamless integration of technology into the fabric of the modern workplace. This Panel will discuss how CIOs can drive innovation, enhance cybersecurity measures, and foster a flexible and inclusive work environment to meet the challenges and opportunities presented by the future of work.
8:55 AM - 9:25 AM MST
WORKSHOP 1 - Never-ending, Unacceptable Levels of Risk, How do We Sleep at Night?
We invest a lot into patching and correction of misconfigurations, but we never really reach a point where we can say we have a tolerable amount of risk in our environment. We feel deeply, at a certain point, with a skilled enough attacker, or one bad decision, a breach is likely to happen. This can be incredibly taxing.
Join this session to discuss:
- Can I define a “tolerable” amount of risk?
- How do I measure more within my security program (and why should that matter)
- What helps me sleep the most at night?
Presented by: Lacework
![]()
8:55 AM - 9:25 AM MST
WORKSHOP 2 - Resilience Planning: Disaster Recovery & Business Continuity
This session will explore strategies to ensure organizational resilience against unexpected disruptions, focusing on crafting robust disaster recovery and continuous business operations plans. We will discuss how to assess risks, implement effective recovery tactics, and maintain operational integrity under various scenarios. The session aims to equip organizations with the tools and knowledge to swiftly recover from setbacks while minimizing impact on operations, ensuring a seamless path to business as usual.
Presented by: Torq
9:35 AM - 10:05 AM MST
WORKSHOP 1 - Predict, Explain, Retain: Better Data Analysis for Better Security Programs
Getting past the hype of AI and ChatGPT, there are huge benefits to practical (and less sexy) applications of AI that can make the lives of security practitioners better. And despite all the buzzwords and overpromises coming from our industry today, there actually are real and meaningful ways AI tools will help security professionals make better risk decisions, faster and more accurately in order to mitigate risk in tangible ways for the business. In this talk, we’ll show some examples of how AI can help predict risk, cut through complexity when making risk decisions and even help to retain senior staff while keeping them focused on the tasks that matter most.
Speaker: Nathan Wenzler, Chief Security Strategist, Tenable
Presented by: Tenable
![]()
9:35 AM - 10:05 AM MST
WORKSHOP 2 - Cyber Defense Strategies for Earlier Detection and Faster Response
Delve into the flaws of the traditional cybersecurity landscape and how a modern SOC should focus on outcome-based services without relying on logs or the cost and complexity of a SIEM.
Presented by: LMNTRIX
![]()
10:05 AM - 10:20 AM MST
SINC NETWORKING & REFRESHMENT BREAK
Circle back with your Peers on the content so far while grabbing a coffee or tea and a snack
10:20 AM - 10:50 AM MST
WORKSHOP 1 - Building The 'True' Software-Defined Data Centers
The software-defined data center (SDDC) is a concept in which all data center infrastructure is virtualized and delivered as a service. Control is fully automated through software, allowing hardware configuration to be maintained through automated policies. SDDC advances virtualization and cloud computing by supporting both legacy enterprise applications and new cloud computing services. It thus provides a solid base for using public, private, and hybrid clouds. By abstracting applications from hardware, SDDC allows apps to run anywhere and even move from place to place. It also allows for greater automation within a data center and faster, simple orchestration across centers.
10:20 AM - 10:50 AM MST
WORKSHOP 2 - AI in the Enterprise- Identifying Winning Business Cases
Enterprises have hordes of data and many opportunities to integrate other data sources. But readying data for AI experimentation is expensive and requires an iterative approach. This session will focus on finding the best opportunities to experiment with AI and on applying agile practices in machine learning initiatives.
11:00 AM - 11:30 AM MST
WORKSHOP 1 - How to Build a Five Star Data Protection Program
It’s time to get serious about data protection. With breaches on the rise and sensitive data widely distributed across cloud and mobility, organizations need a solid data protection strategy more than ever. But how should you structure your data protection program to ensure you can deliver game-changing security?
Join this engaging session to learn the best strategy for building a five-star data protection program. You’ll get guidance from industry experts on cutting-edge approaches that not only provide airtight protection, but drastically reduce cost and complexity.
This session will cover:
- What the best architecture for data protection is
- How to gain complete visibility to all your sensitive data
- Strategies to secure top uses cases around data in motion and at rest
- Data protection best practices
Speaker: Tyrin Ford, Director, Data Protection, Zscaler
Presented by: Zscaler
11:00 AM - 11:30 AM MST
WORKSHOP 2 - Addressing Scalability and Security Challenges in Enterprise Container Management
In this session, we’ll explore best practices for orchestrating, securing, and scaling containerized applications in the enterprise. We’ll discuss the importance of container orchestration, delve into the challenges of security, and examine methods for efficient provisioning. Additionally, we’ll cover the essentials of network and communication strategies, the importance of robust monitoring and logging techniques, and strategies for managing persistent storage. Our goal is to provide actionable insights for implementing a robust container management ecosystem that enhances deployment speed and reliability.
11:40 AM - 12:20 PM MST
PANEL - Sustainable IT Trends and Lessons Learned for Early Momentum
Join our nonprofit partner SustainableIT.org for this panel session to learn:
- How companies are making sustainability part of their IT/Business alignment, and achieving success.
- How companies should be thinking about and addressing the growing number of government regulations around sustainability.
- How your organization can gain quick sustainability wins and start making progress on initiatives today, regardless of where you are on your journey.
Brought to you by SustainableIT
Panelist: Jason Simpson, VP of Engineering, Choice Hotels

![]()
12:20 PM - 1:20 PM MST
SINC NETWORKING LUNCH
Open seating, Buffet-style lunch. Serving food for all tastes, Palates, and preferences. Vegan, vegetarian, halal options available
1:20 PM - 1:50 PM MST
PRESENTATION - How the Technology Leader has Become the Business Leader
Technology leaders are now key players in strategic decision-making processes. Their insights are crucial for identifying new business opportunities, assessing risks, and making informed decisions that balance innovation with sustainability. They play a vital role in developing strategies that capitalize on digital transformation, data analytics, and artificial intelligence to drive growth and efficiency.
Speaker: Shawna DelHierro, Former CTO, Sportsman Warehouse
2:0 PM - 2:50 PM MST
ROUNDTABLE + PANEL - Translating Cybersecurity Strategy into Action
During this session, we will discuss how to bridge the gap between theoretical cybersecurity frameworks and their practical implementation within organizations. It offers insights into effectively translating high-level security strategies into actionable steps that can be understood and executed by IT teams and security professionals. The session emphasizes the importance of aligning cybersecurity measures with business objectives to ensure both are resilient against evolving digital threats.
3:00 PM - 3:30 PM MST
PRESENTATION - Using AI to Enhance Customer and Employee Journeys
In today’s dynamic business environment, companies face the imperative of delivering instant answers and assistance to customers engaging with digital channels. This informative discussion addresses the vital elements needed to produce tangible results to meet this demand. While AI tools and smart agents can minimize human intervention, professionals across sales, marketing, and customer service must navigate customer interactions and team collaboration in new ways. In this chat we will address the challenges to be aware of in the strategic deployment of these technologies and steps to take to ensure they deliver expected value.
Speaker: Mike Egli, CX Client Principal, RingCentral
Presented by: RingCentral
![]()
3:30 PM - 3:45 PM MST
SINC NETWORKING & REFRESHMENT BREAK
Circle back with your Peers on the content so far while grabbing a coffee and a snack
3:50 PM - 4:20 PM MST
WORKSHOP 1 - Achieving the Benefits of Converged Endpoint Management
Managing endpoint risk and compliance is more challenging today than ever before. Today’s CISOs have to manage risk from many thousands of globally distributed, heterogeneous assets, while also responding to ever increasing audit scrutiny and regulatory compliance requirements.
Join this session, Achieving the Benefits of Converged Endpoint Management, to learn more about how to:
- Identify & remediate risks that create the greatest exposure.
- Assess & measure unknown vulnerabilities.
- Maximize IT budgets and staffing during economic uncertainty.
- Enhance existing investment in strategic technology vendors.
Presented by: Tanium
![]()
3:50 PM - 4:20 PM MST
WORKSHOP 2 - Balancing AI With The Indispensable Human Element in Cybersecurity
Artificial Intelligence is a pervasive part of our lives today, and cybersecurity teams and adversaries alike have learned to harness the speed and power of machines to strengthen their capabilities. With machine learning becoming one of the most important tools of defense, leaders must balance the overwhelming speed and accuracy advantage of AI with the need for measured and intuitive interactions with a real-world human element.
Join this session to discuss:
- What these trends mean for the hands-on practitioner
- What happens when the velocity of innovation outpaces the capabilities of human intellect
- The evolving role of automation in the effective practice of securing our digital world
Presented by: SentinelOne
![]()
4:25 PM - 5:15 PM MST
ROUNDTABLE + PANEL: Driving The Business Through Technology
It is no secret that technology is changing the fabric of business operations and outcomes, and collaboration between IT and the business is more important than ever before. The conversation is no longer about how to align IT with the business, however, in many cases, technology is still viewed as a commodity rather than an enabler. So what can we do to successfully change this mindset both within our own organizations and across the industry as a whole? During this session, we will discuss the various challenges IT and digital leaders face when undergoing this cultural shift.
Moderator: Jason Frame, CIO, Southern Nevada Health District
Panelist: Kondal Yennaram, VP, Enterprise Technology, LPL Financial

![]()
6:00 PM - 7:00 PM MST
SINC NETWORKING RECEPTION
Engage your Peers over canapés and cocktails
7:00 PM - 9:00 PM MST
SINC NETWORKING & ENGAGEMENT DINNER
8:00 AM - 8:50 AM MST
SINC IT LEADERS NETWORKING BREAKFAST
Full Breakfast and lots of coffee available!
9:00 AM - 9:50 AM MST
CISO PANEL - Integrating Cybersecurity and Business Strategy
This Panel will discuss how to seamlessly blend cybersecurity measures with overarching business objectives. The panel will explore practical approaches for ensuring that cybersecurity investments enhance business value, support growth, and align with long-term strategic goals. This dialogue aims to equip participants with strategies to make cybersecurity a driving force behind business success, rather than an afterthought.
Moderated by: Cyera
Panelists:
Sasha Pereira, CISO, WASH Multifamily Laundry Systems
Nadeem Iftikhar, CISO, NextNav

![]()
10:00 AM - 10:30 AM MST
PRESENTATION - Low Hanging Fruit – Improving AD Security for the Easy Win
Threat actors, Red-Teams, and Ransomware have been abusing Active Directory for years. In fact, attackers have compromised or leveraged AD in 100% of the successful ransomware attacks over the last 3 years. This discussion will discuss new technologies to help you visualize the risk in your AD and add a layer of security around this very important part of enterprise infrastructure.
10:30 AM - 10:45 AM MST
SINC NETWORKING & REFRESHMENT BREAK
Circle back with your Peers on the content so far while grabbing a coffee and a snack
10:50 AM - 11:20 AM MST
WORKSHOP 1 - A Data Driven Journey: Insights and Lessons Learned
Everyone’s journey to being data-driven is unique. It’s like making an apple pie. It’s easy to get the ingredients, but you need to know how to put together the right recipe for a great apple pie. In this interactive discussion I will share insights and lessons learned in leading data modernization initiatives and in sharing the journey with customers. Data literacy, culture, governance, quality, technology stack modernization and architecture are all ingredients in driving towards the right data driven recipe. The discussion will include tips and tricks for reducing friction points and how to build the right recipe for your organization.
10:50 AM - 11:20 AM MST
WORKSHOP 2 - From On-Prem to the Cloud: Protect Your Apps and APIs
The result of digital transformation: It’s easier to do business with your customers and partners. But with new architectures, web apps and APIs now deployed from on-prem servers to the cloud, it is harder than ever to get a holistic view of all of these potentially vulnerable assets – never mind defend them.
What are your biggest challenges today in defending these diverse assets? What are the known gaps in your current defenses? What are you seeking in the future to defend your apps and APIs?
Topics covered will include:
- How are adversaries preying upon unprotected web apps and APIs?
- How are traditional web application firewalls deployed, and what are they missing?
- What does the future look like with unified web app and API security solutions?
11:30 AM - 12:00 PM MST
PRESENTATION - Maximizing Value Vs Minimizing Cost- Building a more Valuable IT Department
To meet the speed and agility demands of digital business, CIOs are transforming their IT departments and shifting a growing share of IT work from projects to products. At the same time, growth in business-led IT has expanded the span of employees across the enterprise who are responsible for technology initiatives.
This session will explore a cost management model and discuss how evolving IT cost management efforts to focus on value over pure cost will reduce (and even eliminate) reactive calls to cut IT costs. This session will provide a model and tactics to elevate the maturity of IT to focus on value over costs, while still meeting the business directives.
12:00 PM - 1:00 PM MST
SINC NETWORKING LUNCH
West Executive Advisory Council

Shawnna DelHierro
CTO
Sportsman Warehouse (Former)

Nadeem Iftikhar
CISO
NextNav

Roger Franke
Vice President of IT
Aramark
Elena Seiple
VP, CISO
Zillow

Niel Nickolaisen
CIO
Sorenson Communications

Paul Duchouquette
CIO
FDH Aero

Chris Stoneley
CISO
Cathay Bank

Robert Martin
CTO
Bridgepay Network Solutions

Vijay Mohnish
CTO
Ria Financial

Marcel Spitalnik
Director of Business Transformation
Danone

Adip Dsouza
VP of Technology
Merchants Mortgage & Trust Corporation

Sylvia Jessen
Director of IT
University of Utah School of Medicine

Tanweer Surve
Executive Director, Cloud Control Management
Wells Fargo
Interested in sponsoring? Please submit a request.
Submit RequestForum Sponsors
- Partner Sponsor
- platinum Sponsor
- gold Sponsor
- silver Sponsor

Partner
SustainableIT
For too long, sustainability has been someone else’s problem to solve. As technology leaders, we drive digital transformation programs that unlock the art of the possible. Together we can define sustainable transformation programs, author best practices and frameworks, set standards and certifications for governance, provide education and training, and raise awareness for environmental and societal programs that make our organizations and the world sustainable for generations to come.
It’s time technology leaders take a stand for sustainability, as one.
Learn More
platinum
RingCentral
RingCentral is a leading global provider of cloud-based business communications and collaboration solutions that seamlessly combine phone, messaging, video meetings, and contact center. RingCentral empowers customers with AI-powered conversation intelligence that unlocks insights from their interaction data to accelerate business outcomes. With decades of expertise in reliable and secure cloud communications, RingCentral has earned the trust of millions of customers and thousands of partners worldwide.
Learn More
gold
Cyera
Cyera is the data security company that gives businesses context and control over their most valuable asset: data. As a pioneer in Data Security Posture Management, Cyera instantly provides companies visibility over their sensitive data, context over the risk it represents and their security exposure, and automated remediation to reduce the attack surface and ensure operational resilience. We are redefining the way companies secure their data.
Learn More
gold
Lacework
Lacework is the data-driven security platform for the cloud. The Lacework Polygraph Data Platform automates cloud security at scale so our customers can innovate with speed and safety. Only Lacework can collect, analyze, and accurately correlate data across an organization’s AWS, Azure, GCP, and Kubernetes environments, and narrow it down to the handful of security events that matter. Customers all over the globe depend on Lacework to drive revenue, bring products to market faster and safer and consolidate point security solutions into a single platform.
Learn More
gold
Tenable
Tenable®, Inc. is the Cyber Exposure company. Over 30,000 organizations around the globe rely on Tenable to understand and reduce cyber risk. As the creator of Nessus®, Tenable extended its expertise in vulnerabilities to deliver the world’s first platform to see and secure any digital asset on any computing platform. Tenable customers include more than 50 percent of the Fortune 500, more than 30 percent of the Global 2000 and large government agencies.
Learn More
gold
LMNTRIX
LMNTRIX is the leader in intelligence led security-as-a-service. Working as a seamless, scalable extension of customer security operations, LMNTRIX offers a single MDR solution called Active Defense that blends their cyber defense platform called LMNTRIX XDR with innovative security technologies, nation-state grade threat intelligence and world-renowned Cyber Defence Centers. With this approach, LMNTRIX eliminates the complexity and burden of cyber security for organizations struggling to prepare for, prevent and respond to cyberattacks.
Learn More
gold
Torq
Torq is your security product’s favorite security product. Torq Hyperautomation unifies and automates the entire security infrastructure to deliver unparalleled protection and productivity.
More from Torq:
Torq Hyperautomation: A Quantum Leap Forward
How Hyperautomation Reinvents Security Case Management
Learn Moregold
Zscaler
Zscaler enables the world’s leading organizations to securely transform their networks and applications for a mobile and cloud first world. Its flagship services, Zscaler Internet Access and Zscaler Private Access, create fast, secure connections between users and applications, regardless of device, location, or network. Zscaler services are 100% cloud-delivered and offer the simplicity, enhanced security, and improved user experience that traditional appliances or hybrid solutions are unable to match. Used in more than 185 countries, Zscaler operates the world’s largest cloud security platform, protecting thousands of enterprises and government agencies from cyberattacks and data loss.
Learn More
gold
SentinelOne
SentinelOne is a pioneer in delivering autonomous security for the endpoint, datacenter and cloud environments to help organizations secure their assets with speed and simplicity. SentinelOne unifies prevention, detection, response, remediation, and forensics in a single platform powered by artificial intelligence. With SentinelOne, organizations can detect malicious behavior across multiple vectors, rapidly eliminate threats with fully-automated integrated response and to adapt their defenses against the most advanced cyberattacks.
More from SentinelOne:
Learn More
gold
Tanium
Tanium, the industry’s only provider of converged endpoint management (XEM), leads the paradigm shift in legacy approaches to managing complex security and technology environments. Only Tanium unifies teams and workflows and protects every endpoint from cyber threats by integrating IT, Operations, Security, and Risk into a single platform that delivers comprehensive visibility across devices, a unified set of controls, and a common taxonomy for a single shared purpose: to protect critical information and infrastructure at scale.
Learn More
silver
Egnyte
Connect better. Protect better. Do more together.
Egnyte transforms businesses through smarter content allowing organizations to connect, protect, and unlock value from all their content. Our content governance platform delivers smart content collaboration and governance in the cloud or on-premises to thousands of businesses around the world even the most regulated industries.
silver
Claroty
Claroty empowers organizations to secure cyber-physical systems across industrial (OT), healthcare (IoMT), and enterprise (IoT) environments: the Extended Internet of Things (XIoT). The company’s unified platform integrates with customers’ existing infrastructure to provide a full range of controls for visibility, risk and vulnerability management, threat detection, and secure remote access. Backed by the world’s largest investment firms and industrial automation vendors, Claroty is deployed by hundreds of organizations at thousands of sites globally.
Learn More







